Datadog DevSecOps


Standard Operating Procedure For Datadog Code Security Implementation
(SAST + SCA + Secrets + IaC Scanning using GitHub Integration)
1. Purpose
This SOP defines a standard, automated, and repeatable process to configure Datadog Code Security for GitHub repositories.
- Static code vulnerability detection (SAST)
- Dependency risk analysis (SCA)
- Secret exposure detection
- Infrastructure as Code (IaC) misconfiguration detection
- PR-based security enforcement
- Centralized vulnerability visibility inside Datadog
2. Scope
In Scope:
- GitHub repository integration
- Datadog Code Security activation
- Scan configuration
- PR comment enablement
- Security policy enforcement
- Vulnerability review workflow
Out of Scope:
- GitHub account creation
- Datadog account creation
- CI/CD pipeline creation
- Application deployment configuration
3. Target Audience
- DevOps Engineers
- DevSecOps Engineers
- SRE Teams
- Platform Engineering Teams
4. Assumptions & Prerequisites
Infrastructure:
- GitHub repository available
- Datadog account active
- Repository contains application code, dependency files, and IaC files
Access:
- Admin access to GitHub repository
- Admin access to Datadog Code Security
5. High-Level Architecture
Developer ↓ Push / PR GitHub Repository ↓ Datadog Code Security Engine ↓ Security Dashboard ↓ PR Comments + Merge Gate ↓ Deployment Pipeline
6. Implementation Steps (With Navigation)
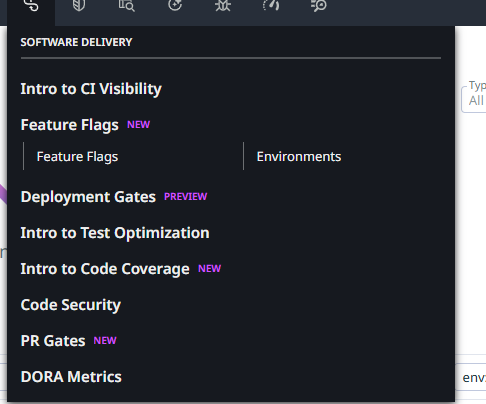
7. PHASE 1 — Navigate to Code Security
Datadog → Software Delivery → Code Security
8. PHASE 2 — Enable Code Security Setup
Datadog → Security → Code Security → Setup
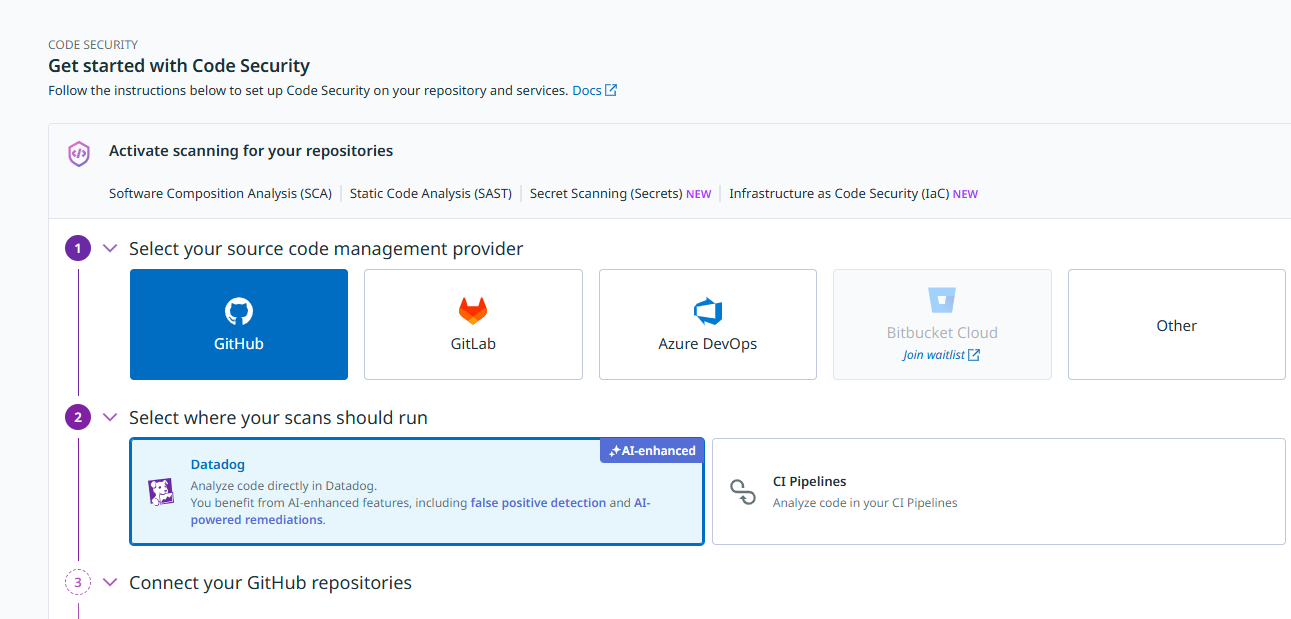
9. PHASE 3 — Select Source Code Provider
Select GitHub as source control provider.
10. PHASE 4 — Select Where Scans Should Run
- Datadog (AI-enhanced) — Recommended
- CI Pipelines
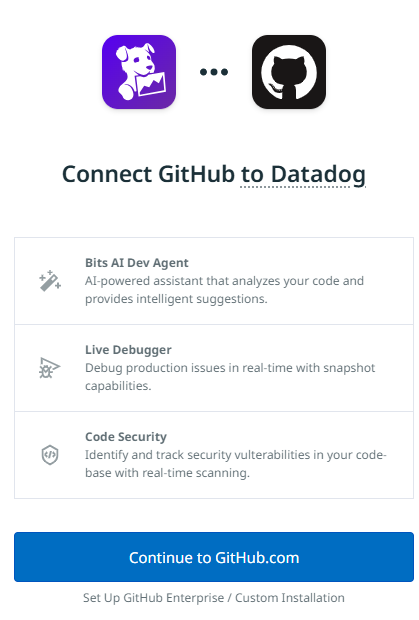
11. PHASE 5 — Connect GitHub Account
- Add GitHub Account
- Authorize Datadog GitHub App
- Select required repositories
- Grant permissions
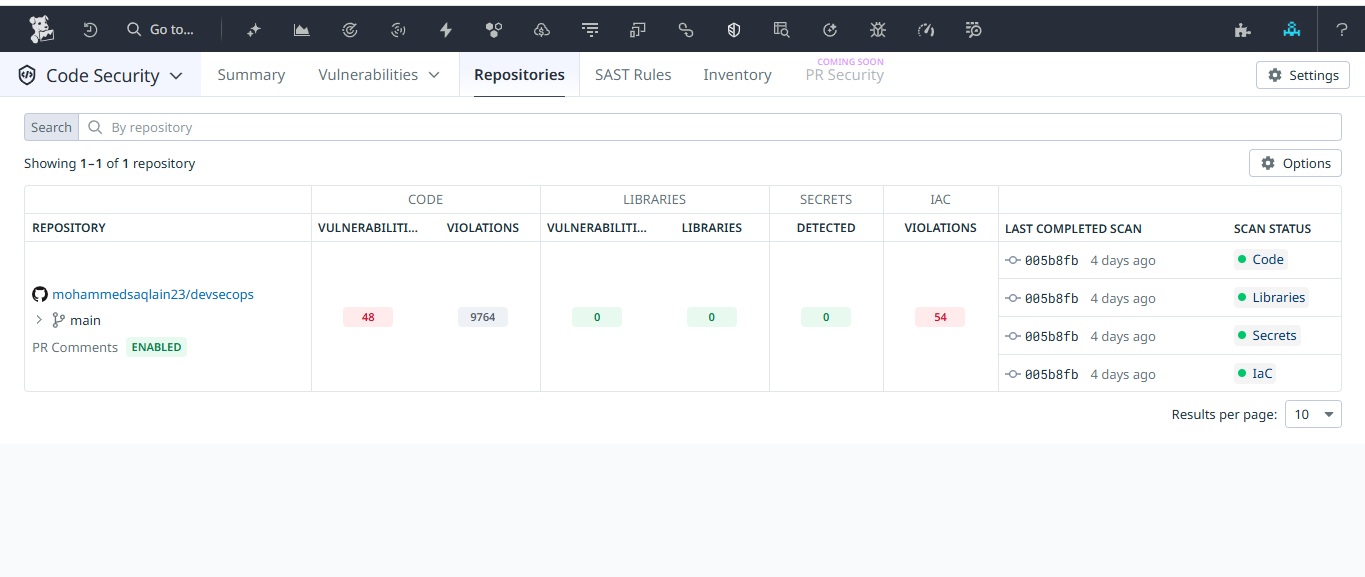
12. PHASE 6 — Repository Configuration
Select repository: mohammedsaqlain23/devsecops
- PR Comments → ENABLED
- Branch scanned → main
| Module | Detects |
|---|---|
| SAST | Code-level vulnerabilities |
| SCA | Vulnerable dependencies |
| Secrets | Hardcoded credentials |
| IaC | Misconfigured infrastructure |
14. PHASE 8 — Trigger First Scan
git add . git commit -m "Initial commit" git push origin main
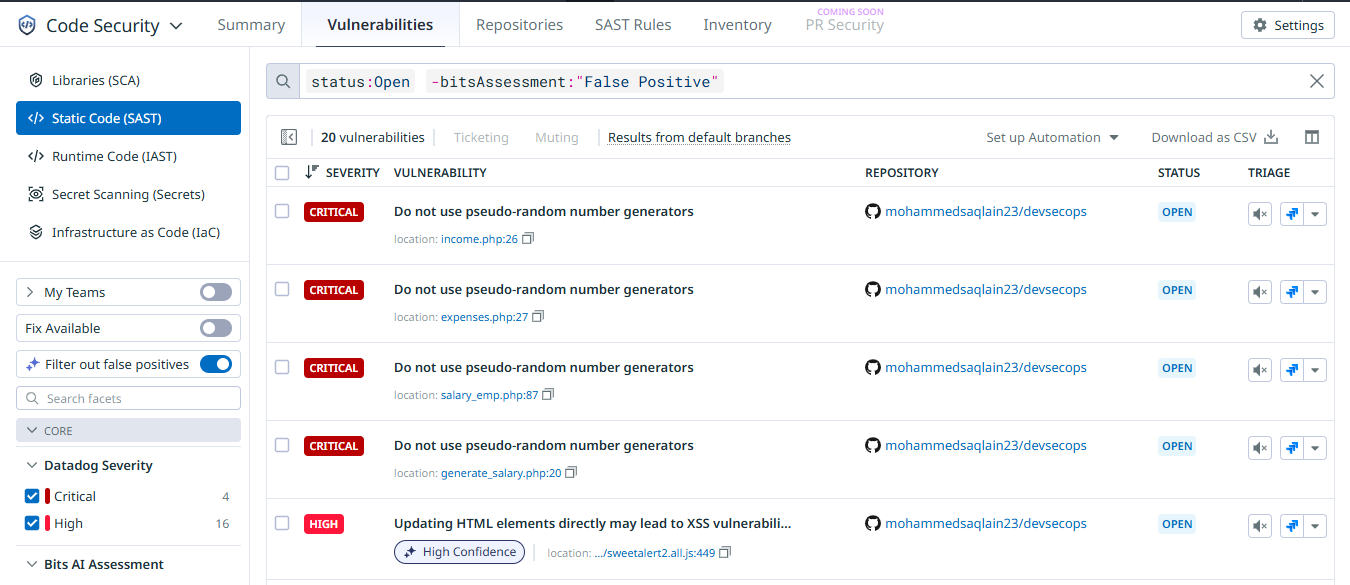
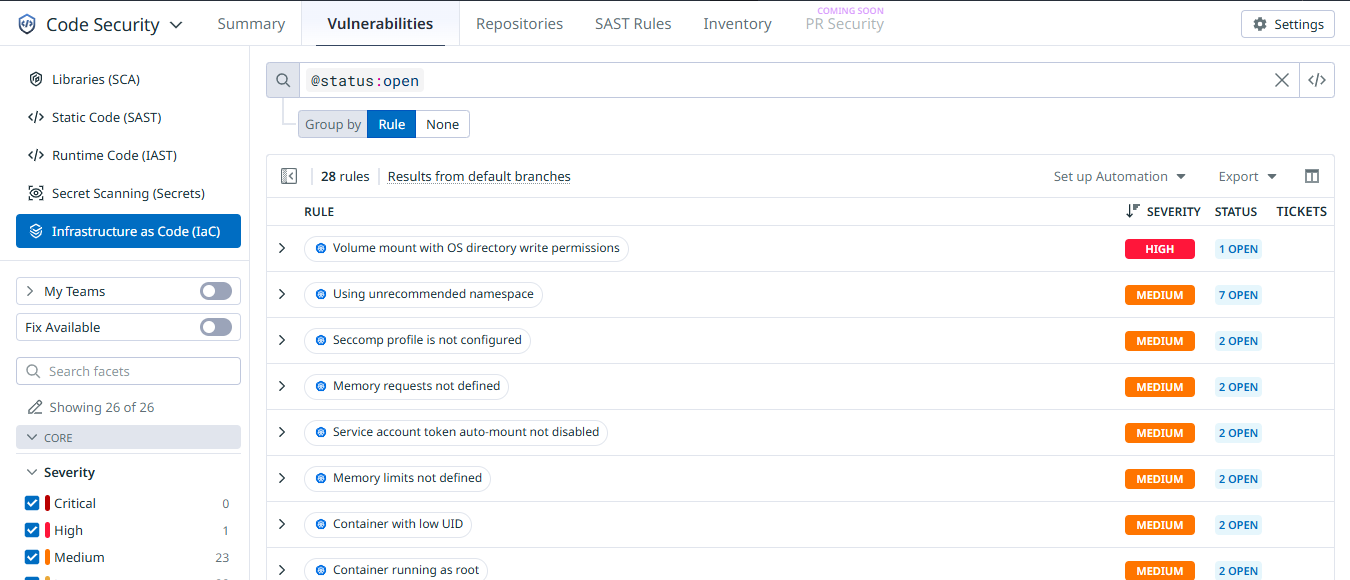
15. PHASE 9 — Review Findings
- Code Vulnerabilities
- Code Violations
- Libraries
- Secrets
- IaC Violations
16. PHASE 10 — Enable PR Security (Shift-Left)
Ensure PR Comments are enabled to enforce early remediation.
17. PHASE 11 — Security Policy Configuration
| Severity | Action |
|---|---|
| Critical | Block merge |
| High | Fix before release |
| Medium | Fix within SLA |
| Low | Monitor |
18. PHASE 12 — Remediation Workflow
git checkout -b fix/security-issue
19. PHASE 13 — Merge Gate Enforcement
- No Critical vulnerabilities
- No exposed secrets
- No High-risk IaC violations
20. Post-Implementation Validation
- Scan status → Green
- Reduced vulnerability count
- PR comments functioning
- No secret exposures
21. Security & Best Practices
- Enable branch protection
- Require PR approvals
- Use environment variables for secrets
- Update dependencies regularly
- Review weekly reports
22. Limitations
- SAST does not detect runtime issues
- False positives may occur
- IaC scanning does not replace CSPM tools
23. Conclusion
- Automated repository scanning
- Multi-layer security detection
- AI-enhanced vulnerability analysis
- Shift-left PR enforcement
- Enterprise-grade merge gating
- Continuous security governance
Contact
- Patrick Schmidt — patrick@airowire.com
- Piyush Choudhary — piyush@airowire.com
- Dr. Shivanand Poojara — shivanand@airowire.com